Featured Content
Phishing Simulation
Our self-service phishing simulation platform allows you to test employee awareness to real phishing attacks, and reinforce security principles through instant feedback.
Self-service Phishing Simulation:
- Real-world attacks: Each phishing series contains 20+ phishing attacks borrowed from current, real-world examples to help your employees learn to recognize real attacks, and avoid falling for them.
- Randomized scheduling options: Choose from various scheduling options, including randomization of attacks sent for each employee with random schedules for each to minimize pattern recognition.
- Instant feedback: Employees that engage with phishing attacks will be immediately shown reminders not to be vigilant when reading and engaging with email.
- Reinforcement: Employees that engage with phishing will be provided additional training to reinforce awareness.
- Tracking: Tracking allows you to monitor employee engagement with phishing attacks and to target those who need additional education.
- Auditable: Tracking also allows you to provide evidence that phishing simulation is being performed on a continual basis.
- Fresh: We are always adding new content and tools to keep employees on their toes.
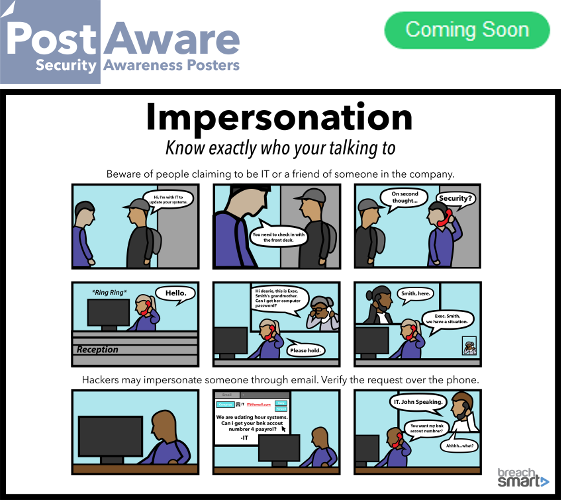
Advanced Curated Social Engineering
Beyond standard phishing simulation, we offer custom-designed social engineering services, which optionally include vectors tailored and personalized to your environments and employees. Vectors include sophisticated spear phishing, in-person attacks, and phone-based attacks.
This service may be coupled with the phishing simulation above, to provide maximal security awareness to employees.
Curated Social Engineering vectors include:
- Custom spear-phishing: Custom-design phishing attack vectors that leverage research for personalization.
- Pretext calling: Call scripts delivered over the phone to attempt to elicit sensitive information or risky behavior.
- Planted media: USBs (memory sticks or devices), CDs, or DVDs delivered to employees or locations, with or without pretext.
- Social networking: Vectors that exploit the trust relationships users have with their social media platforms.
- Tailgating: Testing awareness of employees to in-person attacks to the importance of vigilance with physical threats.
BreachSmart Portal
BreachSmart is a simple training platform that allows you to create on-going training and phishing campaigns to email your employees links to videos for them watch, to track progress, and report on success.
To launch a training campaign as simple as this:
- Upload and/or select users to train
- Pick a training video series from the content library.
- Select a frequency (daily, weekly).
- Press go and monitor progress.
- Identify and Isolate employees that have not watched videos, and designate them for additional reinforcement.
- Produce progress reports on your training program
For a demo of our platform, click here.
Benefits
There are many benefits to using BreachSmart. We list some of them below:
- BreachSmart training is designed to be non-disruptive. The idea is to train frequently, but only for a minute at the time (like the length of a commercial or short YouTube video).
- BreachSmart will not disrupt productivity, while raising and maintaining awareness, and increasing resilience to Cyber-attacks.
- BreachSmart training is not boring. The videos are designed to be at least mildly entertaining which increases message retention by viewers.
- Our videos are short to match the short attention span of today’s media consumer, again to maximize retention
- Our platform allows companies to track training progress and identify employees who need additional encouragement to stay on top of their training requirements
- Our platform allows companies to report on security awareness training to demonstrate and prove commitment to security awareness training to boards, auditors and regulators
- Our content subject matter is designed by experienced pen-testers whose experience leveraging employees in pen-testing engagement informs our content.
How to get started with BreachSmart
Getting started is simple:
- Sign-up for an account
- Add users (upload emails)
- Select a training series and create a campaign
- Remove videos that are not desired (if needed)
- Select a frequency (daily, weekly)
- Modify dates (if need be)
- Press go and monitor progress
- Generate training progress reports
Contact us and we’ll help you get started today!
Custom Content and Licensing
Inquire about licensing our content for use in your own learning management system.
And our talented team of media specialists are available to customize and personalize our content to your needs. We are also available to create custom content, just for you.
Contact us for more info.
Credibility
Our training content was designed by the experienced pen-testers from Illumant. Illumant is a seasoned security assessment and penetration testing firm with approximately 20 years of experience providing pen testing, social engineering, and security assessment services to financial institutions, hospitals, cities, tech companies, energy companies ... all verticals. In its security penetration testing engagements Illumant conducts simulated cyber-attacks against its clients and leveraging gaps in employee security awareness to propagate attacks. The simulated cyber-attacks mimic the attacks crafted by real black hat hackers. As such, Illumant is keenly aware of the gaps in education that can create vulnerabilities and that put organizations at risk.
Illumant has provided in-person training based on the materials in BreachSmart to Fortune 500 companies.
Given our experience, this training is designed to:
- harden the employees against cyber-attacks
- help employees learn to identify and avoid cyber threats like phishing and social engineering
- to help employees protect their employers.
Illumant's experience is invaluable the relevance of our training videos.
Learn more about Illumant and its assessment and pen-testing services here.