Navigating Risk in a Distributed Digital Environment
As organizations continue to modernize their infrastructure, cloud and hybrid environments have become the foundation of digital transformation. Businesses are leveraging public cloud platforms, private infrastructure, and on-premises systems to increase flexibility, scalability, and performance.
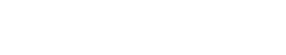
However, this shift has introduced a new set of cybersecurity challenges. The traditional network perimeter has dissolved, data is more distributed than ever, and responsibility for security is now shared across multiple stakeholders. Securing cloud and hybrid environments requires a fundamentally different approach than legacy IT models.
The Complexity of Cloud and Hybrid Environments
Cloud and hybrid architectures are inherently complex. Organizations often operate across multiple cloud providers while maintaining legacy systems on-premises. This creates a fragmented environment where visibility, control, and consistency can be difficult to maintain.
Security teams must manage:
- Multiple platforms with different security models
- Distributed workloads across regions and environments
- Diverse identity and access management systems
- Rapidly changing infrastructure and configurations
This complexity increases the likelihood of misconfigurations, which remain one of the leading causes of cloud security incidents.
The Shared Responsibility Model
One of the most misunderstood aspects of cloud security is the shared responsibility model. Cloud providers are responsible for securing the underlying infrastructure, but customers are responsible for securing their data, applications, and configurations.
This division can create gaps if not clearly understood.
For example:
- The cloud provider secures the physical data center and hardware
- The customer is responsible for access controls, data protection, and application security
Many breaches occur not because the cloud platform was compromised, but because security responsibilities on the customer side were not properly implemented.
Identity as the New Security Perimeter
In cloud and hybrid environments, identity has become the primary control point. Users, applications, and services all require access to resources, often from various locations and devices.
Common identity-related risks include:
- Overly permissive access rights
- Lack of multi-factor authentication
- Credential theft and reuse
- Poor lifecycle management of accounts
Without strong identity governance, attackers can gain access to critical systems without triggering traditional network-based defenses.
Misconfigurations and Visibility Gaps
Misconfigurations continue to be one of the most significant risks in cloud environments. Examples include:
- Publicly exposed storage buckets
- Open security groups or firewall rules
- Unrestricted administrative access
- Disabled logging and monitoring
These issues are often unintentional but can expose sensitive data or create entry points for attackers.
Visibility is another major challenge. With assets spread across multiple environments, security teams may struggle to maintain a complete and accurate inventory of systems, data, and access permissions.
Securing Data Across Environments
Data in cloud and hybrid environments is constantly moving between systems, users, and locations. Protecting that data requires consistent controls regardless of where it resides.
Key challenges include:
- Ensuring encryption in transit and at rest
- Managing data classification and sensitivity levels
- Preventing unauthorized data sharing or exfiltration
- Maintaining compliance with regulatory requirements
Without centralized data governance, organizations risk losing control over where sensitive information is stored and how it is accessed.
Third-Party and Supply Chain Risk
Cloud adoption often involves reliance on third-party services, integrations, and vendors. Each additional connection introduces potential risk.
Security concerns include:
- Vulnerabilities in third-party applications
- Excessive permissions granted to external services
- Limited visibility into vendor security practices
- Dependency on external systems for critical operations
Organizations must extend their security posture beyond their own environment to include partners and service providers.
Strategies for Strengthening Cloud and Hybrid Security

Addressing these challenges requires a combination of technology, process, and governance.
Establish Strong Identity and Access Controls
Implement least-privilege access, enforce multi-factor authentication, and regularly review permissions. Identity should be tightly controlled and continuously monitored.
Adopt a Zero Trust Approach
Zero trust assumes that no user or system is inherently trusted. Every access request must be verified based on identity, device, and context.
Improve Configuration Management
Use automated tools to continuously scan for misconfigurations and enforce security baselines across all environments. Infrastructure should be deployed using secure, repeatable templates.
Enhance Visibility and Monitoring
Centralize logging and monitoring to gain visibility across cloud and on-premises systems. Real-time alerts can help detect suspicious activity before it escalates.
Protect Data Consistently
Apply encryption, data loss prevention, and classification policies across all environments. Data security should not vary based on location.
Strengthen Vendor Risk Management
Assess third-party security practices, limit access to only what is necessary, and continuously monitor integrations for risk.
The Importance of a Unified Security Strategy
Cloud and hybrid environments cannot be secured with isolated tools or fragmented processes. Organizations need a unified security strategy that spans all platforms and aligns with business objectives.
This includes:
- Centralized governance and policy enforcement
- Integration between security tools and platforms
- Collaboration between IT, security, and business teams
- Continuous assessment and improvement
A cohesive approach reduces complexity and improves the organization’s ability to respond to emerging threats.
Final Thoughts
Cloud and hybrid environments offer significant advantages, but they also require a shift in how security is approached. The disappearance of the traditional perimeter, combined with increased complexity and shared responsibility, creates new risks that cannot be addressed with legacy security models.
Organizations that succeed in this environment are those that prioritize visibility, enforce strong identity controls, and implement consistent security practices across all systems.
Security in the cloud is not a one-time effort. It is an ongoing process that must evolve alongside the organization’s infrastructure and threat landscape.