Why Layered Controls — Not Just Email Security — Are Critical
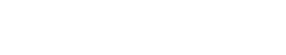
Business Email Compromise (BEC) continues to be one of the most financially damaging cyber threats organizations face. Unlike ransomware or malware-based attacks, BEC schemes often involve no malicious attachments, no suspicious links, and no obvious technical indicators. Instead, they exploit trust, authority, and routine financial processes.
In many cases, attackers gain access to a legitimate email account — sometimes an executive’s, sometimes a vendor’s. Once inside, they monitor communications and wait for the right moment to request a wire transfer or alter payment instructions. When the request comes from a real account, detecting fraud based solely on email becomes extremely difficult.
That is why preventing wire fraud requires layered defenses and strong financial controls — not just email filtering tools.
The Core Problem: Email Alone Is Not a Reliable Verification Method
When an account is compromised, the attacker’s message:
- Comes from a legitimate email address
- Appears in an existing email thread
- Matches the tone and signature of the sender
- References real invoices or ongoing projects
To a finance or accounts payable employee, the request may look completely normal. Even experienced professionals can struggle to distinguish a fraudulent request from a legitimate one when relying on email alone.
This is precisely why email should never be the sole approval mechanism for financial transactions.
Layered Defense: Building Strong Financial Controls
The most effective protection against BEC-related wire fraud is a structured, multi-layered control environment that assumes email may be compromised.
1. Mandatory Out-of-Band Verification for Vendor Payment Changes
Any request to change vendor banking information should trigger a required verification process.
Best practice includes:
- Calling a previously verified phone number on file
- Not using the phone number listed in the change request email
- Documenting the verification conversation
- Requiring secondary approval before updating payment records
This single control has prevented countless fraudulent transfers. Attackers depend on organizations failing to independently confirm changes.
2. Wire Validation Prior to Funds Transfer
Before initiating any wire transfer, especially large or unusual ones, organizations should:
- Confirm the wire instructions verbally
- Re-validate beneficiary account details
- Review whether the transaction aligns with typical payment patterns
- Require dual authorization
Even if the request appears urgent, verification must override speed. Fraudsters frequently create urgency to pressure staff into bypassing procedures.
3. Dual Approval and Segregation of Duties
No single individual should control the entire wire process.
Strong internal controls include:
- One person initiates the wire
- A second person reviews and approves
- A third-level approval for high-dollar transfers
Segregation of duties significantly reduces the risk of both external fraud and internal manipulation.
4. Pre-Defined Escalation Protocols for Unusual Requests
Employees should have clear guidance on what constitutes a red flag, such as:
- Requests to bypass normal procedures
- Last-minute payment changes
- Confidential acquisition-related wires
- International transfers to new accounts
When something feels unusual, employees must feel empowered — and expected — to escalate for verification.
5. Strong Email Security and MFA — But Not as the Only Line of Defense
Technical safeguards still matter. Organizations should implement:
- Multi-factor authentication on all email accounts
- Executive and finance account monitoring
- Domain spoofing protections (SPF, DKIM, DMARC)
- Alerts for suspicious login activity
However, even the strongest email security controls cannot eliminate the risk of account compromise entirely. That is why financial process controls must exist independently of email systems.
The Human Factor: Training and Culture
Layered defenses only work if employees understand and respect them.
Training should emphasize:
- Real-world BEC examples
- The importance of verification policies
- How attackers use urgency and authority
- That verifying with leadership is never insubordinate
Executives must model this behavior by supporting verification requirements — even if it delays a transaction. When leadership prioritizes security over speed, employees follow suit.
Why Layered Controls Matter More Than Detection Alone
The reality is simple: it is often impossible to determine whether a wire request from a compromised email account is legitimate based on email content alone.
Instead of relying solely on detection, organizations must design processes that assume compromise is possible and require independent validation.
Layered defenses create friction — but that friction protects assets.
A five-minute phone call to verify wire instructions can prevent a six-figure loss.
Final Thoughts
Business Email Compromise succeeds when organizations trust email more than they trust process.
The most effective defense is not just better spam filters or smarter AI — it is disciplined financial controls, independent verification, segregation of duties, and a culture that supports questioning unusual requests.
When layered defenses are in place, even a fully compromised email account does not automatically lead to wire fraud.
And in today’s threat environment, that distinction can mean the difference between resilience and significant financial loss.